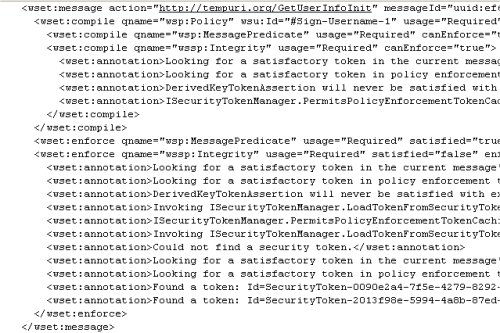
This is from the policy tracing file created by my client where I am fiddling around and trying to use policy to sign with a use usernametoken. Here’s a screenshot and then just a copy/paste so you can read the actual message. My point here is not to get help ,but to show you the level of detailed information that is output by WSE2 so that if you need to do some problem solving, you’ve got gobs of info. Pretty educational stuff.
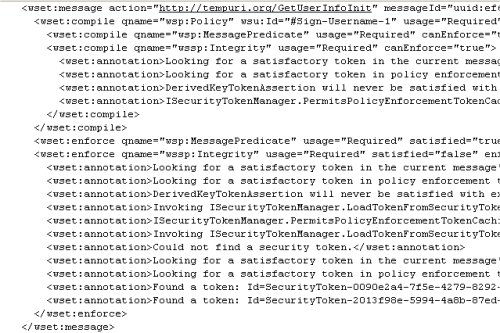
<wset:message action=”http://tempuri.org/GetUserInfoInit” messageId=”uuid:ef64131b-543d-4df6-a50e-ec90cd6a6e5d” appDomain=”FieldApplication_TESTS_UI.exe” time=”2004-09-28T11:21:45.7968275-04:00″>
<wset:compile qname=”wsp:Policy” wsu:Id=”#Sign-Username-1″ usage=”Required” canEnforce=”true”>
<wset:compile qname=”wsp:MessagePredicate” usage=”Required” canEnforce=”true” />
<wset:compile qname=”wssp:Integrity” usage=”Required” canEnforce=”true”>
<wset:annotation>Looking for a satisfactory token in the current message’s token collection…</wset:annotation>
<wset:annotation>Looking for a satisfactory token in policy enforcement token cache…</wset:annotation>
<wset:annotation>DerivedKeyTokenAssertion will never be satisfied with existing tokens during compilation or enforcement. Not satisfied with this token: Id=SecurityToken-8e8a551b-5120-4506-902b-8e3abd171fef, Type=UsernameToken</wset:annotation>
<wset:annotation>ISecurityTokenManager.PermitsPolicyEnforcementTokenCaching is set to false in the token manager registered for this token type. We will assume this assertion is enforceable. Failures will be revealed during enforcement.</wset:annotation>
</wset:compile>
</wset:compile>
<wset:enforce qname=”wsp:MessagePredicate” usage=”Required” satisfied=”true” enforced=”false” />
<wset:enforce qname=”wssp:Integrity” usage=”Required” satisfied=”false” enforced=”true”>
<wset:annotation>Looking for a satisfactory token in the current message’s token collection…</wset:annotation>
<wset:annotation>Looking for a satisfactory token in policy enforcement token cache…</wset:annotation>
<wset:annotation>DerivedKeyTokenAssertion will never be satisfied with existing tokens during compilation or enforcement. Not satisfied with this token: Id=SecurityToken-8e8a551b-5120-4506-902b-8e3abd171fef, Type=UsernameToken</wset:annotation>
<wset:annotation>Invoking ISecurityTokenManager.LoadTokenFromSecurityTokenAssertion from the token manager registered for this token type.</wset:annotation>
<wset:annotation>ISecurityTokenManager.PermitsPolicyEnforcementTokenCaching is set to true in the token manager registered for this token type. A token will be loaded from the token manager and cached for subsequent message enforcement.</wset:annotation>
<wset:annotation>Invoking ISecurityTokenManager.LoadTokenFromSecurityTokenAssertion from the token manager registered for this token type.</wset:annotation>
<wset:annotation>Could not find a security token.</wset:annotation>
<wset:annotation>Looking for a satisfactory token in the current message’s token collection…</wset:annotation>
<wset:annotation>Looking for a satisfactory token in policy enforcement token cache…</wset:annotation>
<wset:annotation>Found a token: Id=SecurityToken-0090e2a4-7f5e-4279-8292-6fcdc78a78f2, Type=UsernameToken</wset:annotation>
<wset:annotation>Found a token: Id=SecurityToken-2013f98e-5994-4a8b-87ed-2b80ade897f6, Type=DerivedKeyToken</wset:annotation>
</wset:enforce>
</wset:message>